General Aptitude
Ravi had ______ younger brother who taught at ______ university. He was widely regarded as ______ honorable man. Select the option with the correct sequence of articles to fill in the blanks.
The CEO's decision to downsize the workforce was considered myopic because it sacrificed long-term stability to accommodate short-term gains. Select the most appropriate option that can replace the word "myopic" without changing the meaning of the sentence.
The average marks obtained by a class in an examination were calculated as 30.8. However, while checking the marks entered, the teacher found that the marks of one student were entered incorrectly as 24 instead of 42. After correcting the marks, the average becomes 31.4. How many students does the class have?
Consider the relationships among P, Q, R, S, and T:
• P is the brother of Q.
• S is the daughter of Q.
• T is the sister of S.
• R is the mother of Q.
The following statements are made based on the relationships given above.
(1) R is the grandmother of S.
(2) P is the uncle of S and T.
(3) R has only one son.
(4) Q has only one daughter.
Which one of the following options is correct?
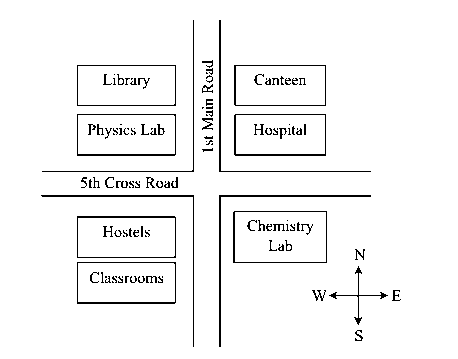
According to the map shown in the figure, which one of the following statements is correct? [Note: The figure shown is representative.]
"I put the brown paper in my pocket along with the chalks, and possibly other things. I suppose every one must have reflected how primeval and how poetical are the things that one carries in one's pocket: the pocket-knife, for instance the type of all human tools, the infant of the sword. Once I planned to write a book of poems entirely about the things in my pocket. But I found it would be too long: and the age of the great epics is past."
(From G.K. Chesterton's "A Piece of Chalk")
Based only on the information provided in the above passage, which one of the following statements is true?
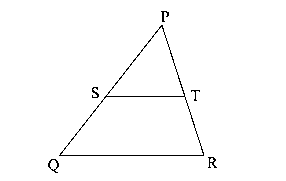
In the diagram, the lines QR and ST are parallel to each other. The shortest distance between these two lines is half the shortest distance between the point P and line QR. What is the ratio of the area of the triangle PST to the area of the trapezium SQRT? [Note: The figure shown is representative.]
A fair six-faced dice, with the faces labelled '1', '2', '3', '4', '5', and '6', is rolled thrice. What is the probability of rolling '6' exactly once?
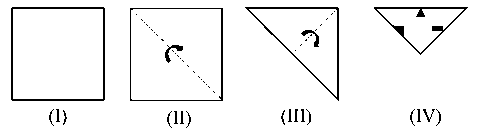
A square paper, shown in figure (I), is folded along the dotted lines as shown in the figures (II) and (III). Then a few cuts are made as shown in figure (IV). Which one of the following patterns will be obtained when the paper is unfolded? [Note: The figures shown are representative.]
A shop has 4 distinct flavors of ice-cream. One can purchase any number of scoops of any flavor. The order in which the scoops are purchased is inconsequential. If one wants to purchase 3 scoops of ice-cream, in how many ways can one make that purchase?
Computer Science and Information Technology
Suppose a program is running on a non-pipelined single processor computer system. The computer is connected to an external device that can interrupt the processor asynchronously. The processor needs to execute the interrupt service routine (ISR) to serve this interrupt. The following steps (not necessarily in order) are taken by the processor when the interrupt arrives:
(i) The processor saves the content of the program counter.
(ii) The program counter is loaded with the start address of the ISR.
(iii) The processor finishes the present instruction.
Which ONE of the following is the CORRECT sequence of steps?
Which ONE of the following statements is FALSE regarding the symbol table?
Which ONE of the following techniques used in compiler code optimization uses live variable analysis?
Consider a demand paging memory management system with 32-bit logical address, 20-bit physical address, and page size of 2048 bytes. Assuming that the memory is byte addressable, what is the maximum number of entries in the page table?
A schedule of three database transactions T1, T2, and T3 is shown. and denote read and write of data item A by transaction , . The transaction aborts at the end. Which other transaction(s) will be required to be rolled back? Schedule:
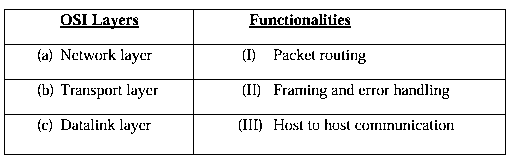
Identify the ONE CORRECT matching between the OSI layers and their corresponding functionalities as shown.
is a function from A to B, is a function from B to C, and their composition defined as is a mapping from A to C. If and are onto (surjective) functions, which ONE of the following is TRUE about the function
Let G be any undirected graph with positive edge weights, and T be a minimum spanning tree of G. For any two vertices, and , let and be the shortest distances between and in G and T, respectively. Which ONE of the options is CORRECT for all possible G, T, u and v?
Consider the following context-free grammar G, where S, A, and B are the variables (non-terminals), a and b are the terminal symbols, S is the start variable, and the rules of G are described as:
S aaB | Abb,
A a | aA,
B b | bB.
Which ONE of the languages L(G) is accepted by G?
Consider the following recurrence relation: for , . Which ONE of the following options is CORRECT?
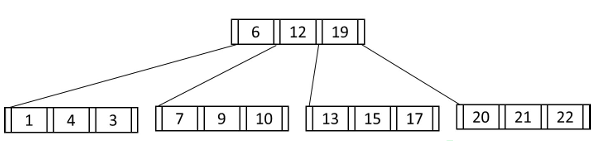
Consider the following B+ tree with 5 nodes, in which a node can store at most 3 key values. The value 23 is now inserted in the B+ tree. Which of the following options(s) is/are CORRECT?
Consider the 3-way handshaking protocol for TCP connection establishment. Let the three packets exchanged during the connection establishment be denoted as P1, P2, and P3, in order. Which of the following option(s) is/are TRUE with respect to TCP header flags that are set in the packets?
Consider the given system of linear equations for variables x and y, where k is a real-valued constant: and . Which of the following option(s) is/are CORRECT?
Let X be a 3-variable Boolean function that produces output as '1' when at least two of the input variables are '1'. Which of the following statement(s) is/are CORRECT, where a, b, c, d, e are Boolean variables?
The number -6 can be represented as 1010 in 4-bit 2's complement representation. Which of the following is/are CORRECT 2's complement representation(s) of -6?
Which of the following statement(s) is/are TRUE for any binary search tree (BST) having n distinct integers?
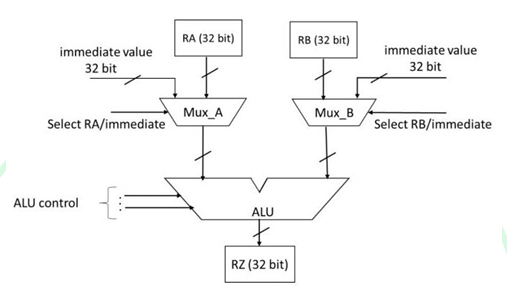
A partial data path of a processor is given in the figure, where RA, RB, and RZ are 32-bit registers. Which option(s) is/are CORRECT related to arithmetic operations using the data path as shown?
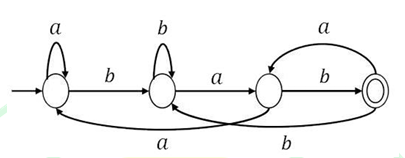
A regular language L is accepted by a non-deterministic finite automaton (NFA) with n states. Which of the following statement(s) is/are FALSE?
Suppose in a multiprogramming environment, the following C program segment is executed. A process goes into I/O queue whenever an I/O related operation is performed. Assume that there will always be a context switch whenever a process requests for an I/O, and also whenever the process returns from an I/O. The number of times the process will enter the ready queue during its lifetime (not counting the time the process enters the ready queue when it is run initially) is ___.
Let S be the set of all ternary strings defined over the alphabet {a, b, c}. Consider all strings in S that contain at least one occurrence of two consecutive symbols, that is, "aa", "bb" or "cc". The number of such strings of length 5 that are possible is ______.
Consider the given function . If the function is differentiable everywhere, the value of b must be ______ (rounded off to one decimal place).
A box contains 5 coins: 4 regular coins and 1 fake coin. When a regular coin is tossed, the probability P(head) = 0.5 and for a fake coin, P(head) = 1. You pick a coin at random and toss it twice, and get two heads. The probability that the coin you have chosen is the fake coin is ______ (rounded off to two decimal places).
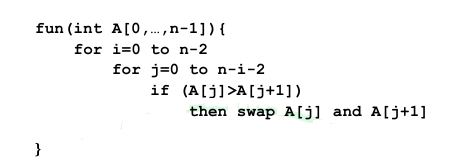
The pseudocode of a function fun () is given below: Let A[0, ...,29] be an array storing 30 distinct integers in descending order. The number of swap operations that will be performed, if the function fun () is called with A[0, ...,29] as argument, is ______.
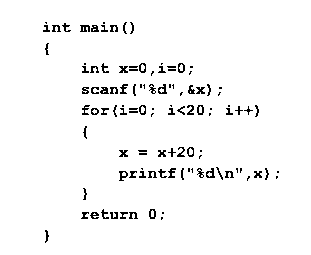
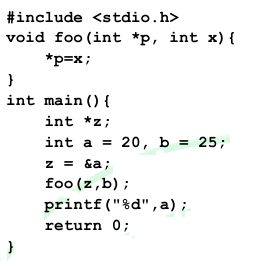
The output of the given C program is ______.
The height of any rooted tree is defined as the maximum number of edges in the path from the root node to any leaf node. Suppose a Min-Heap T stores 32 keys. The height of T is ______.
Consider a memory system with 1M bytes of main memory and 16K bytes of cache memory. Assume that the processor generates 20-bit memory address, and the cache block size is 16 bytes. If the cache uses direct mapping, how many bits will be required to store all the tag values? [Assume memory is byte addressable, , .]
A processor has 64 general-purpose registers and 50 distinct instruction types. An instruction is encoded in 32 bits. What is the maximum number of bits that can be used to store the immediate operand for the given instruction?
A computer has two processors, and . Four processes P1, P2, P3, P4 with CPU bursts of 20, 16, 25, and 10 milliseconds, respectively, arrive at the same time and these are the only processes in the system. The scheduler uses non-preemptive priority scheduling, with priorities decided as follows:
• uses priority of execution for the processes as, , i.e., and have highest and lowest priorities, respectively.
• uses priority of execution for the processes as, , i.e., and have highest and lowest priorities, respectively.
A process is scheduled to a processor , if the processor is free and no other process is waiting with higher priority. At any given point of time, a process can be allocated to any one of the free processors without violating the execution priority rules. Ignore the context switch time. What will be the average waiting time of the processes in milliseconds?
Consider two relations describing teams and players in a sports league:
• teams(tid, tname): tid, tname are team-id and team-name, respectively
• players(pid, pname, tid): pid, pname, and tid denote player-id, player-name and the team-id of the player, respectively.
Which ONE of the following tuple relational calculus queries returns the name of the players who play for the team having tname as 'MI'?
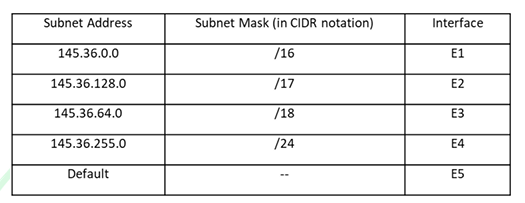
A packet with the destination IP address 145.36.109.70 arrives at a router whose routing table is shown. Which interface will the packet be forwarded to?
Let A be a matrix as given. . What are the eigenvalues of the matrix ?
Consider the following four variable Boolean function in sum-of-product form , where the value of the function is computed by considering as a 4-bit binary number, where denotes the most significant bit and denotes the least significant bit. Note that there are no don't care terms. Which ONE of the following options is the CORRECT minimized Boolean expression for F?
Let G (V, E) be an undirected and unweighted graph with 100 vertices. Let d(u, v) denote the number of edges in a shortest path between vertices u and v in V. Let the maximum value of d(u, v), u, v ∈ V such that u ≠ v, be 30. Let T be any breadth-first-search tree of G. Which ONE of the given options is CORRECT for every such graph G?
Consider the following two languages over the alphabet {a, b}:
and
. Which ONE of the following statements is CORRECT?
Consider the following two languages over the alphabet {a, b, c}, where m and n are natural numbers:
.
Which ONE of the following statements is CORRECT?
Which of the following statement(s) is/are TRUE while computing First and Follow during top down parsing by a compiler?
Consider a relational schema team(name, city, owner), with functional dependencies {name → city, name → owner}. The relation team is decomposed into two relations, t1(name, city) and t2(name, owner). Which of the following statement(s) is/are TRUE?
Which of the following predicate logic formulae/formula is/are CORRECT representation(s) of the statement: "Everyone has exactly one mother"? The meanings of the predicates used are:
• mother(y, x): y is the mother of x
• noteq(x, y): x and y are not equal
A = {0, 1, 2, 3, ... } is the set of non-negative integers. Let F be the set of functions from A to itself. For any two functions, , we define for every number n in A. Which of the following is/are CORRECT about the mathematical structure (F, )?
Consider the following deterministic finite automaton (DFA) defined over the alphabet, . Identify which of the following language(s) is/are accepted by the given DFA.
A disk of size 512M bytes is divided into blocks of 64K bytes. A file is stored in the disk using linked allocation. In linked allocation, each data block reserves 4 bytes to store the pointer to the next data block. The link part of the last data block contains a NULL pointer (also of 4 bytes). Suppose a file of 1M bytes needs to be stored in the disk. Assume, and . The amount of space in bytes that will be wasted due to internal fragmentation is ______.
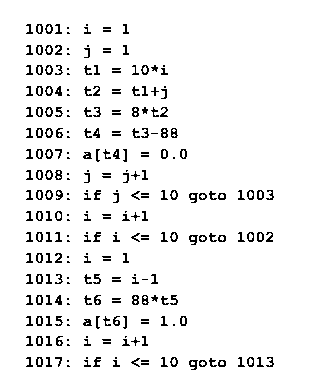
Refer to the given 3-address code sequence. This code sequence is split into basic blocks. The number of basic blocks is ______.
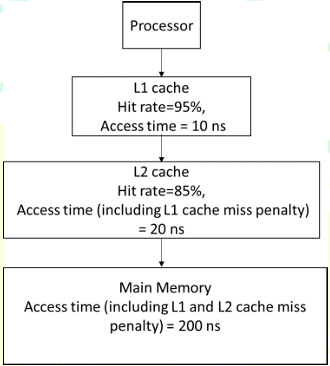
A computer has a memory hierarchy consisting of two-level cache (L1 and L2) and a main memory. If the processor needs to access data from memory, it first looks into L1 cache. If the data is not found in L1 cache, it goes to L2 cache. If it fails to get the data from L2 cache, it goes to main memory, where the data is definitely available. Hit rates and access times of various memory units are shown in the figure. The average memory access time in nanoseconds (ns) is ________. (rounded off to two decimal places)
In optimal page replacement algorithm, information about all future page references is available to the operating system (OS). A modification of the optimal page replacement algorithm is as follows:
The OS correctly predicts only up to next 4 page references (including the current page) at the time of allocating a frame to a page.
A process accesses the pages in the following order of page numbers:
1, 3, 2, 4, 2, 3, 1, 2, 4, 3, 1, 4.
If the system has three memory frames that are initially empty, the number of page faults that will occur during execution of the process is ______.
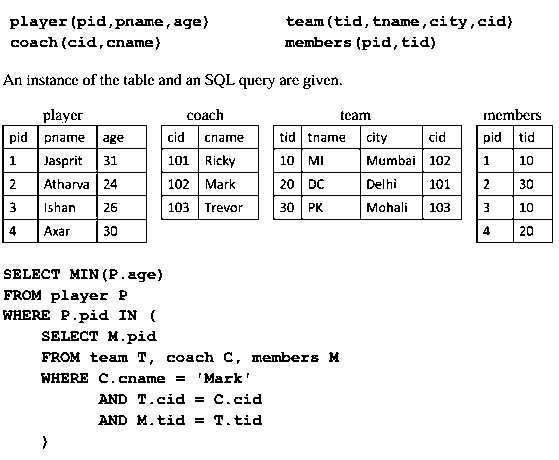
Consider the following database tables of a sports league: . The value returned by the given SQL query is ______.
Suppose a 5-bit message is transmitted from a source to a destination through a noisy channel. The probability that a bit of the message gets flipped during transmission is 0.01. Flipping of each bit is independent of one another. The probability that the message is delivered error-free to the destination is ______ (rounded off to three decimal places).
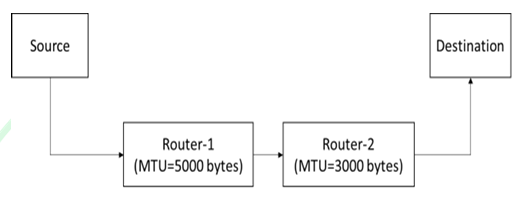
Suppose a message of size 15000 bytes is transmitted from a source to a destination using IPv4 protocol via two routers as shown in the figure. Each router has a defined maximum transmission unit (MTU) as shown in the figure, including IP header. The number of fragments that will be delivered to the destination is ________ . (Answer in integer)
Consider a probability distribution given by the density function . The probability that lies between 2 and 3, i.e., is ______ (rounded off to three decimal places).
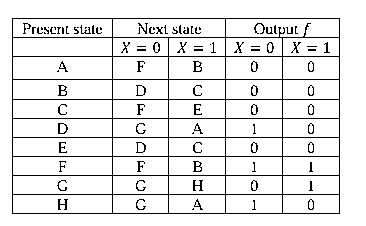
Consider a finite state machine (FSM) with one input X and one output f, represented by the given state transition table. The minimum number of states required to realize this FSM is ______.
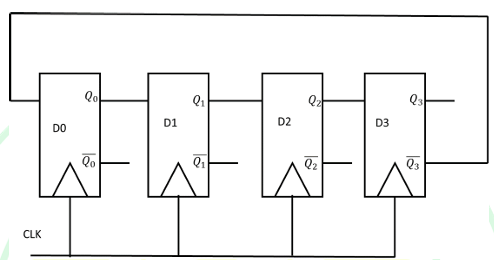
Consider the given sequential circuit designed using D-Flip-flops. The circuit is initialized with some value (initial state). The number of distinct states the circuit will go through before returning back to the initial state is ______.
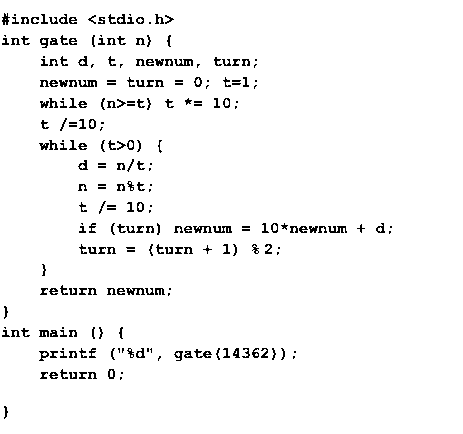
The value printed by the given C program is ______.
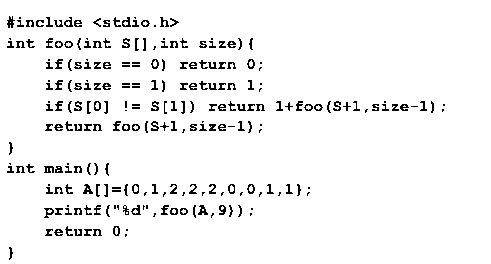
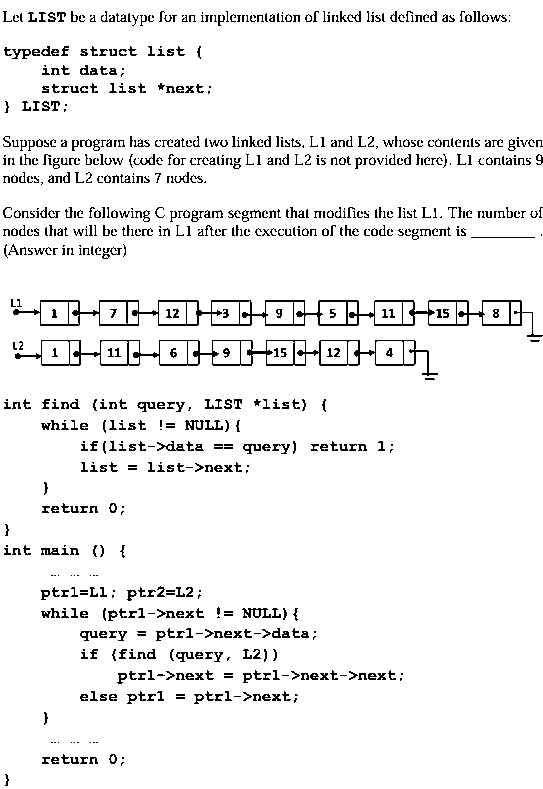
Consider the following C program: The value printed by the given C program is ______.
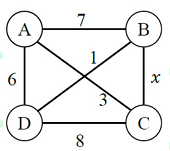
The maximum value of x such that the edge between the nodes B and C is included in every minimum spanning tree of the given graph is ______.
In a double hashing scheme, and are the auxiliary hash functions. The size m of the hash table is 11. The hash function for the i-th probe in the open address table is . The following keys are inserted in the given order: 63, 50, 25, 79, 67, 24. The slot at which key 24 gets stored is ______.