General Aptitude
We reached the station late, and _______ missed the train.
Kind : _______ : : Often : Frequently
(By word meaning)
A series of natural numbers obeys for all integers . If , and , then what is ?
A survey for a certain year found that 90% of pregnant women received medical care at least once before giving birth. Of these women, 60% received medical care from doctors, while 40% received medical care from other healthcare providers. Given this information, which one of the following statements can be inferred with certainty?
Looking at the surface of a smooth 3-dimensional object from the outside, which one of the following options is TRUE?
The country of Zombieland is in distress since more than 75% of its working population is suffering from serious health issues. Studies conducted by competent health experts concluded that a complete lack of physical exercise among its working population was one of the leading causes of their health issues. As one of the measures to address the problem, the Government of Zombieland has decided to provide monetary incentives to those who ride bicycles to work.
Based only on the information provided above, which one of the following statements can be logically inferred with certainty?
Consider two functions of time ,
where .
Now consider the following two statements:
(i) For some , .
(ii) There exists a , such that for all .
Which one of the following options is TRUE?
Which one of the following sentence sequences creates a coherent narrative?
(i) Once on the terrace, on her way to her small room in the corner, she notices the man right away.
(ii) She begins to pant by the time she has climbed all the stairs.
(iii) Mina has bought vegetables and rice at the market, so her bags are heavy.
(iv) He was leaning against the parapet, watching the traffic below.
and are functions of and , respectively, and for all real values of and . Which one of the following options is necessarily TRUE for all and ?
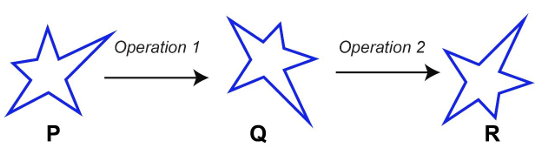
Which one of the options best describes the transformation of the 2-dimensional figure P to Q, and then to R, as shown?
Computer Science and Information Technology
Consider the following statements regarding the front-end and back-end of acompiler.
S1: The front-end includes phases that are independent of the target hardware.
S2: The back-end includes phases that are specific to the target hardware.
S3: The back-end includes phases that are specific to the programming language used in the source code.
Identify the CORRECT option.
Which one of the following sequences when stored in an array at locations forms a max-heap?
Let SLLdel be a function that deletes a node in a singly-linked list given a pointer to the node and a pointer to the head of the list. Similarly, let DLLdel be another function that deletes a node in a doubly-linked list given a pointer to the node and a pointer to the head of the list.
Let denote the number of nodes in each of the linked lists. Which one of the following choices is TRUE about the worst-case time complexity of SLLdel and DLLdel?
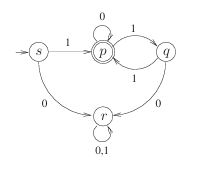
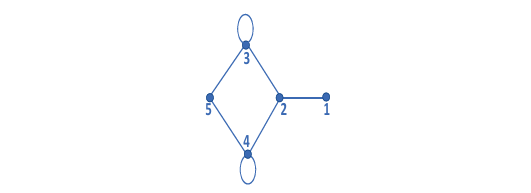
Consider the Deterministic Finite-state Automaton (DFA) shown below. The DFA runs on the alphabet , and has the set of states , with being the start state and being the only final state.
Which one of the following regular expressions correctly describes the language accepted by ?
The Lucas sequence is defined by the recurrence relation:
, for , with and .
Which one of the options given is TRUE?
Which one of the options given below refers to the degree (or arity) of a relation in relational database systems?
Suppose two hosts are connected by a point-to-point link and they are configured to use Stop-and-Wait protocol for reliable data transfer. Identify in which one of the following scenarios, the utilization of the link is the lowest.
Let
and .
Let and denote the determinants of the matrices and , respectively.
Which one of the options given below is TRUE?
Consider the following definition of a lexical token id for an identifier in a programming language, using extended regular expressions:
letter [A-Za-z]
digit [0-9]
id letter (letter | digit)
Which one of the following Non-deterministic Finite-state Automata with -transitions accepts the set of valid identifiers? (A double-circle denotes a final state)
An algorithm has to store several keys generated by an adversary in a hash table. The adversary is malicious who tries to maximize the number of collisions. Let be the number of keys, be the number of slots in the hash table, and .
Which one of the following is the best hashing strategy to counteract the adversary?
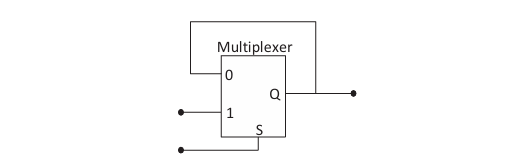
The output of a 2-input multiplexer is connected back to one of its inputs as shown in the figure.
Match the functional equivalence of this circuit to one of the following options.
Which one or more of the following need to be saved on a context switch from one thread (T1) of a process to another thread (T2) of the same process?
Which one or more of the following options guarantee that a computer system will transition from user mode to kernel mode?
Which of the following statements is/are CORRECT?
Which of the following statements is/are INCORRECT about the OSPF (Open Shortest Path First) routing protocol used in the Internet?
Geetha has a conjecture about integers, which is of the form , where is a statement about integers, and is a statement about pairs of integers.
Which of the following (one or more) option(s) would imply Geetha's conjecture?
Which one or more of the following CPU scheduling algorithms can potentially cause starvation?
Let be a real-valued function.
Which of the following statements is/are TRUE?
Let and be functions of natural numbers given by and .
Which of the following statements is/are TRUE?
Let be the adjacency matrix of the graph with vertices .
Let , and be the five eigenvalues of . Note that these eigenvalues need not be distinct.
The value of ___.
The value of the definite integral is ___. (Rounded off to the nearest integer)
A particular number is written as 132 in radix-4 representation. The same number in radix-5 representation is ___.
Consider a 3-stage pipelined processor having a delay of 10 ns (nanoseconds), 20 ns, and 14 ns, for the first, second, and the third stages, respectively. Assume that there is no other delay and the processor does not suffer from any pipeline hazards. Also assume that one instruction is fetched every cycle.
The total execution time for executing 100 instructions on this processor is ___ ns.
A keyboard connected to a computer is used at a rate of 1 keystroke per second. The computer system polls the keyboard every 10 ms (milli seconds) to check for a keystroke and consumes 100 μs (micro seconds) for each poll. If it is determined after polling that a key has been pressed, the system consumes an additional 200 μs to process the keystroke. Let denote the fraction of a second spent in polling and processing a keystroke.
In an alternative implementation, the system uses interrupts instead of polling. An interrupt is raised for every keystroke. It takes a total of 1 ms for servicing an interrupt and processing a keystroke. Let denote the fraction of a second spent in servicing the interrupt and processing a keystroke.
The ratio is ___. (Rounded off to one decimal place)
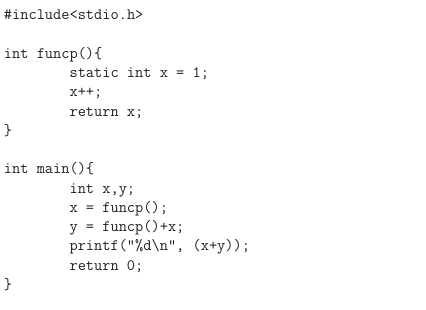
The integer value printed by the ANSI-C program given below is ___.
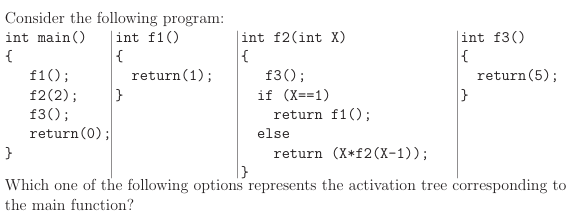
Consider the control flow graph shown.
Which one of the following choices correctly lists the set of live variables at the exit point of each basic block?
Consider the two functions incr and decr shown below.
incr(){
wait(s);
X = X+1;
signal(s);
}
decr(){
wait(s);
X = X-1;
signal(s);
}
There are 5 threads each invoking incr once, and 3 threads each invoking decr once, on the same shared variable X. The initial value of X is 10.
Suppose there are two implementations of the semaphore s, as follows:
I-1: s is a binary semaphore initialized to 1.
I-2: s is a counting semaphore initialized to 2.
Let V1, V2 be the values of X at the end of execution of all the threads with implementations I-1, I-2, respectively.
Which one of the following choices corresponds to the minimum possible values of V1, V2, respectively?
Consider the context-free grammar below
,
where and are non-terminals, and and are terminal symbols. The starting non-terminal is .
Which one of the following statements is CORRECT?
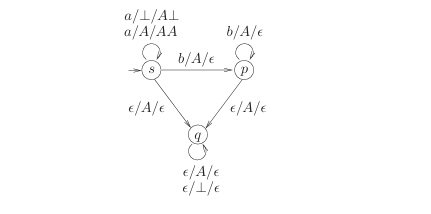
Consider the pushdown automaton (PDA) below, which runs on the input alphabet , has stack alphabet , and has three states , with being the start state. A transition from state to state , labelled , where is an input symbol or , is a stack symbol, and is a string of stack symbols, represents the fact that in state , the PDA can read from the input, with on the top of its stack, pop from the stack, push in the string on the stack, and go to state . In the initial configuration, the stack has only the symbol in it. The PDA accepts by empty stack.
Which one of the following options correctly describes the language accepted by ?
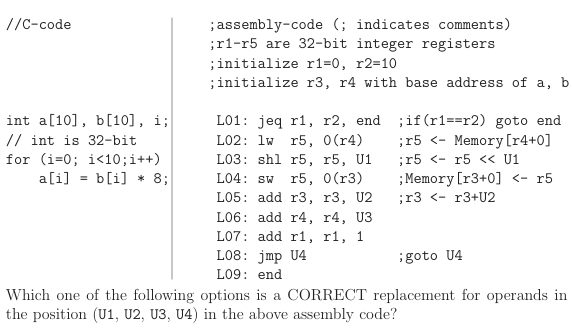
Consider the given C-code and its corresponding assembly code, with a few operands U1–U4 being unknown. Some useful information as well as the semantics of each unique assembly instruction is annotated as inline comments in the code. The memory is byte-addressable.
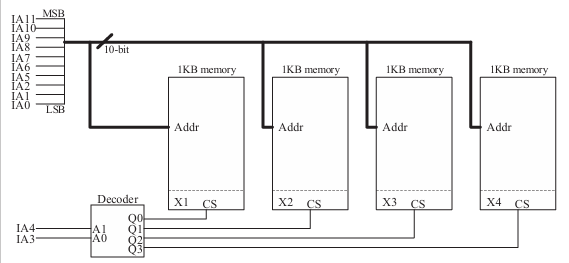
A 4 kilobyte (KB) byte-addressable memory is realized using four 1 KB memory blocks. Two input address lines (IA4 and IA3) are connected to the chip select (CS) port of these memory blocks through a decoder as shown in the figure. The remaining ten input address lines from IA11–IA0 are connected to the address port of these blocks. The chip select (CS) is active high. The input memory addresses (IA11–IA0), in decimal, for the starting locations (Addr=0) of each block (indicated as X1, X2, X3, X4 in the figure) are among the options given below. Which one of the following options is CORRECT?
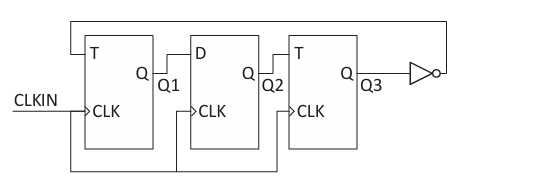
Consider a sequential digital circuit consisting of T flip-flops and D flip-flops as shown in the figure. CLKIN is the clock input to the circuit. At the beginning, Q1, Q2 and Q3 have values 0, 1 and 1, respectively. Which one of the given values of (Q1, Q2, Q3) can NEVER be obtained with this digital circuit?
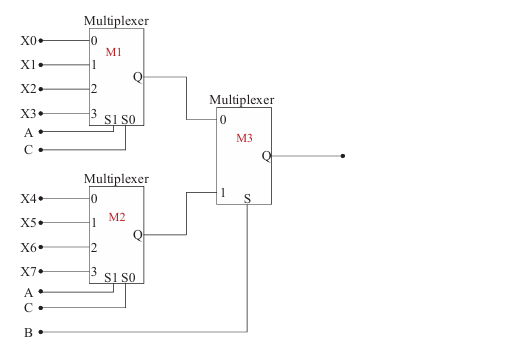
A Boolean digital circuit is composed using two 4-input multiplexers (M1 and M2) and one 2-input multiplexer (M3) as shown in the figure. X0–X7 are the inputs of the multiplexers M1 and M2 and could be connected to either 0 or 1. The select lines of the multiplexers are connected to Boolean variables A, B and C as shown. Which one of the following set of values of will realise the Boolean function ?
Consider the IEEE-754 single precision floating point numbers and . Which one of the following corresponds to the product of these numbers (i.e., ), represented in the IEEE-754 single precision format?
Let be a priority queue for maintaining a set of elements. Suppose is implemented using a max-heap data structure. The operation Extract-Max() extracts and deletes the maximum element from . The operation Insert(, key) inserts a new element key in . The properties of a max-heap are preserved at the end of each of these operations. When contains elements, which one of the following statements about the worst case running time of these two operations is TRUE?
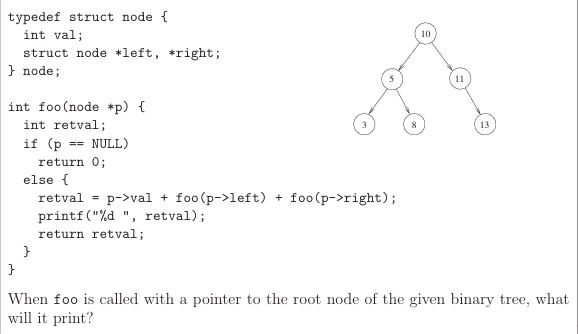
Consider the C function foo and the binary tree shown.
Let , where is a large positive integer greater than 1000. Let be a positive integer less than . Let , be subsets of with and . We say that a permutation of separates from if one of the following is true.
- All members of appear in the permutation before any of the members of .
- All members of appear in the permutation before any of the members of . How many permutations of separate from ?
Let be an onto (or surjective) function, where and are nonempty sets. Define an equivalence relation on the set as
if ,
where . Let be the set of all the equivalence classes under . Define a new mapping as
,
for all the equivalence classes in .
Which of the following statements is/are TRUE?
Suppose you are asked to design a new reliable byte-stream transport protocol like TCP. This protocol, named myTCP, runs over a 100 Mbps network with Round Trip Time of 150 milliseconds and the maximum segment lifetime of 2 minutes. Which of the following is/are valid lengths of the Sequence Number field in the myTCP header?
Let be a set and denote the powerset of . Define a binary operation on as follows:
.
Let . Which of the following statements about is/are correct?
Suppose in a web browser, you click on the www.gate-2023.in URL. The browser cache is empty. The IP address for this URL is not cached in your local host, so a DNS lookup is triggered (by the local DNS server deployed on your local host) over the 3-tier DNS hierarchy in an iterative mode. No resource records are cached anywhere across all DNS servers. Let RTT denote the round trip time between your local host and DNS servers in the DNS hierarchy. The round trip time between the local host and the web server hosting www.gate-2023.in is also equal to RTT. The HTML file associated with the URL is small enough to have negligible transmission time and negligible rendering time by your web browser, which references 10 equally small objects on the same web server. Which of the following statements is/are CORRECT about the minimum elapsed time between clicking on the URL and your browser fully rendering it?
Consider a random experiment where two fair coins are tossed. Let be the event that denotes HEAD on both the throws, be the event that denotes HEAD on the first throw, and be the event that denotes HEAD on the second throw. Which of the following statements is/are TRUE?
Consider functions Function 1 and Function 2 expressed in pseudocode as follows:
Function 1
while n > 1 do
for i = 1 to n do
x = x + 1;
end for
n = floor(n/2);
end while
Function 2
for i = 1 to 100*n do
x = x + 1;
end for
Let and denote the number of times the statement "x = x + 1" is executed in Function 1 and Function 2, respectively. Which of the following statements is/are TRUE?
Let be a simple, finite, undirected graph with vertex set . Let denote the maximum degree of , and let denote the set of available colors. Color the vertices of using the greedy strategy:
Let . Let denote the powerset of . Consider an undirected graph whose vertex set is . For any , is an edge in if and only if (i) , and (ii) either or . For any vertex in , the set of all possible orderings in which the vertices of can be visited in a Breadth First Search (BFS) starting from is denoted by . If denotes the empty set, then the cardinality of is ___.
Consider the following two-dimensional array in the C programming language, which is stored in row-major order:
int D[128][128];
Demand paging is used for allocating memory and each physical page frame holds 512 elements of the array . The Least Recently Used (LRU) page-replacement policy is used by the operating system. A total of 30 physical page frames are allocated to a process which executes the following code snippet:
for (int i = 0; i < 128; i++)
for (int j = 0; j < 128; j++)
D[j][i] *= 10;
The number of page faults generated during the execution of this code snippet is ___.
Consider a computer system with 57-bit virtual addressing using multi-level tree-structured page tables with levels for virtual to physical address translation. The page size is 4 KB () and a page table entry at any of the levels occupies 8 bytes. The value of is ___.
Consider a sequence of elements , and . The following operations are performed on a stack and a queue , both of which are initially empty.
I: push the elements of from to in that order into .
II: enqueue the elements of from to in that order into .
III: pop an element from .
IV: dequeue an element from .
V: pop an element from .
VI: dequeue an element from .
VII: dequeue an element from and push the same element into .
VIII: Repeat operation VII three times.
IX: pop an element from .
X: pop an element from .
The top element of after executing the above operations is ___.
Consider the syntax directed translation given by the following grammar and semantic rules. Here , , and are non-terminals. is the starting non-terminal, and , and are lexical tokens corresponding to input letters "#", "0" and "1", respectively. denotes the synthesized attribute (a numeric value) associated with a non-terminal . and denote occurrences of and on the right hand side of a production, respectively. For the tokens and , and .
The value computed by the translation scheme for the input string is ___. (Rounded off to three decimal places)
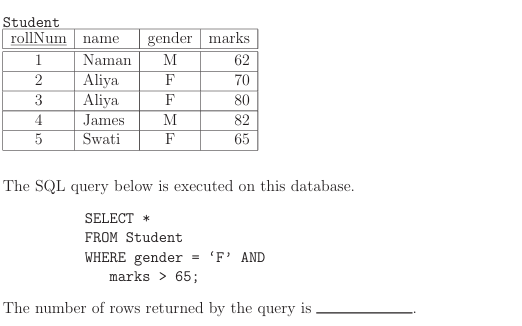
Consider the following table named Student in a relational database. The primary key of this table is rollNum.
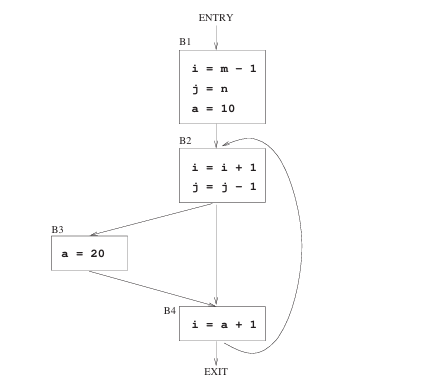
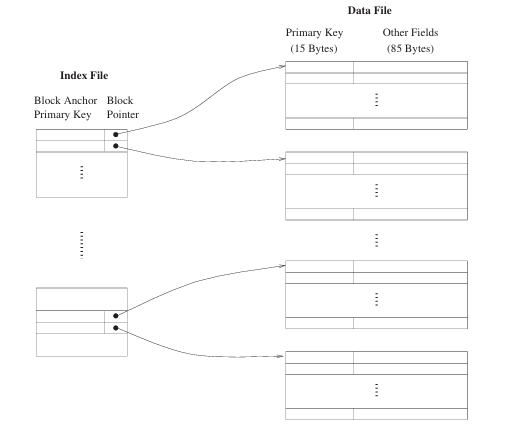
Consider a database of fixed-length records, stored as an ordered file. The database has 25,000 records, with each record being 100 bytes, of which the primary key occupies 15 bytes. The data file is block-aligned in that each data record is fully contained within a block. The database is indexed by a primary index file, which is also stored as a block-aligned ordered file. The figure below depicts this indexing scheme
Suppose the block size of the file system is 1024 bytes, and a pointer to a block occupies 5 bytes. The system uses binary search on the index file to search for a record with a given key. You may assume that a binary search on an index file of blocks takes block accesses in the worst case.
Given a key, the number of block accesses required to identify the block in the data file that may contain a record with the key, in the worst case, is ___.
Consider the language over the alphabet , given below:
.
The minimum number of states in a Deterministic Finite-State Automaton (DFA) for is ___.
An 8-way set associative cache of size 64 KB () is used in a system with 32-bit address. The address is sub-divided into TAG, INDEX, and BLOCK OFFSET. The number of bits in the TAG is ___.
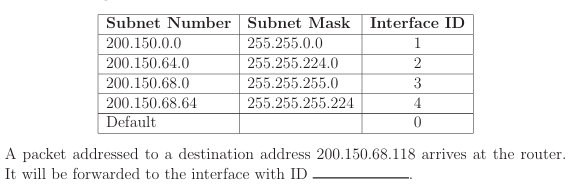
The forwarding table of a router is shown below.